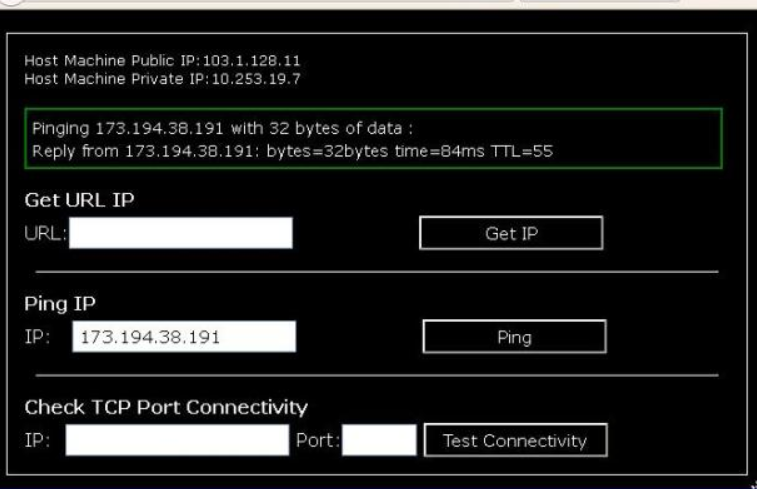
When building web applications with ASP.NET Core, it is often useful to know the IP address of the client/user making the HTTP request. The client IP address can be used for various purposes like implementing IP address based access restrictions, analytics, logging, security etc.
However, determining the actual client IP can be tricky if the requests are going through a proxy server or load balancer. The proxy server handles all the external requests, and the request reaching the ASP.NET Core development Company application will contain the proxy server IP instead of the actual client IP.
In this blog post, we will look at different ways to retrieve the actual client IP address in ASP.NET Core even when requests are coming through a proxy server or load balancer.
ASP.NET Core provides the RemoteIpHeaderAttribute attribute that can be used to tell ASP.NET Core which HTTP request header contains the actual client IP address. If the requests are coming through a proxy, the proxy typically populates the X-Forwarded-For header with the client IP address.
To use RemoteIpHeaderAttribute, first add it to the IHttpContextAccessor service in the Startup.ConfigureServices
method:
Source {csharp}
Copy
services.AddHttpContextAccessor();
services.Configure<ForwardedHeadersOptions>(options =>
{
options.ForwardedHeaders =
ForwardedHeaders.XForwardedFor | ForwardedHeaders.XForwardedProto;
});
Then access the client IP address via HttpContext.Connection.RemoteIpAddress property:
Source {csharp}
Copy
public class HomeController : Controller
{
private readonly IHttpContextAccessor _httpContextAccessor;
public HomeController(IHttpContextAccessor httpContextAccessor)
{
_httpContextAccessor = httpContextAccessor;
}
public IActionResult Index()
{
var remoteIpAddress = _httpContextAccessor
.HttpContext
.Connection
.RemoteIpAddress;
// remoteIpAddress will contain actual client IP
}
}
This works for common proxy servers and load balancers that populate the standard X-Forwarded-For header.
Some proxies may use custom HTTP headers to carry client IP instead of X-Forwarded-For. In such cases, you can configure ASP.NET Core to read client IP from multiple request headers using ForwardedHeadersOptions:
Source {csharp}
Copy
options.ForwardedHeaders =
ForwardedHeaders.XForwardedFor | ForwardedHeaders.XProxyUserIp;
This tells ASP.NET Core to check X-Forwarded-For and then X-Proxy-User-Ip headers for client IP address.
You can also configure it to read IP from a specific custom header:
Source {csharp}
Copy
options.ForwardedHeaders = ForwardedHeaders.MyProxyHeader;
Using Middleware
An alternative to RemoteIpHeaderAttribute is to write custom middleware that reads client IP address from request headers and stores it in the HttpContext.
For example:
Source {csharp}
Copy
public class GetClientIpMiddleware
{
private readonly RequestDelegate _next;
public GetClientIpMiddleware(RequestDelegate next)
{
_next = next;
}
public async Task Invoke(HttpContext context)
{
string ipAddress;
if (context.Request.Headers.ContainsKey(“X-Forwarded-For”))
{
ipAddress = context.Request.Headers[“X-Forwarded-For”].FirstOrDefault();
}
else
{
throw new Exception(“Could not determine client IP address”);
}
context.Connection.RemoteIpAddress = IPAddress.Parse(ipAddress);
await _next(context);
}
}
Register this middleware before your other middleware:
Source {csharp}
Copy
app.UseMiddleware<GetClientIpMiddleware>();
Now client IP will be available via RemoteIpAddress property.
Instead of storing client IP in the HttpContext, you can also directly read it from the request headers wherever needed:
Source {csharp}
Copy
string ipAddress;
if (context.Request.Headers.ContainsKey(“X-Forwarded-For”)) {
ipAddress = context.Request.Headers[“X-Forwarded-For”].FirstOrDefault();
}
This avoids polluting the HttpContext and allows reading IP flexibly on per-request basis.
Issues Behind Multiple Proxies
If the request passes through multiple proxies, the client IP will be stored in X-Forwarded-For header as a list separated by comma. In that case you need to parse this header to extract the first (left-most) IP address which is closest to the client:
Source {csharp}
Copy
var ipList = context.Request.Headers[“X-Forwarded-For”].Split(“,”).ToList();
ipAddress = ipList.FirstOrDefault();
Also note that some proxies may spoil X-Forwarded-For header by adding their own IP incorrectly. In those cases, it may not be possible to reliably determine the client IP.
Diesel is an open-source .NET middleware that tries to normalize HTTP headers coming from various proxies and load balancers. It rewrites headers like X-Forwarded-For to a standard format.
To use Diesel in ASP.NET Core:
Source {csharp}
Copy
services.AddDiesel(options => {
options.ForwardedForHeader = “X-Forwarded-For”;
});
This helps abstract away differences between various proxies and provides a consistent way to retrieve client IP.
Conclusion
Hire Dot NET Core Developers involves finding individuals who can implement various methods for retrieving the actual client IP address in ASP.NET Core applications, even when requests pass through proxies and load balancers. The RemoteIpHeaderAttribute offers a straightforward mechanism but relies on proxies correctly populating standard headers. Custom solutions, such as middleware, provide greater flexibility but require more code. Using Diesel to normalize proxies helps mitigate differences between various proxy implementations. Understanding how proxies function is essential for choosing the appropriate approach for a specific scenario or proxy configuration.